BankOnIT Strengthens Its Advisory Board.
We are excited to announce the addition of Roger Beverage to the BankOnIT Advisory Board.
With over 40 years of experience in the financial industry, including former positions as the CEO of both the Nebraska and Oklahoma Bankers Associations, co-founder and board member of Friends of Traditional Banking, and the Director of the Department of Banking for the State of Nebraska, Roger brings valuable knowledge of the banking industry to our team. Welcome Roger, your expertise will benefit BankOnIT and client bankers.
Regulators See Gaps In Third-party Risk Management.
Federal Reserve Vice Chair Michael Barr commented in January1 that cyber threats are constantly evolving and regulators expect threats to become increasingly disruptive as technology advances and our financial system becomes more interconnected. Barr also commented that regulators “have historically seen gaps” with regard to third-party risk management. He also stated that all Federal bank regulatory agencies adopted interagency guidance last year on management of third-party risk. The guidance is meant to help banks as they strengthen their risk management and may be found here: Interagency Guidance on Third-Party Relationships: Risk Management.
Three Major Corporations Are Setting Regulatory Disclosure Expectations.
Defense company Lockheed Martin, oil field services provider Schlumberger, and equipment rental company United Rentals are the first major businesses to file annual 10-K reports that meet the SEC’s requirement for expanded cyber risk and oversight disclosures. They are setting early expectations for how much companies must disclose about their cybersecurity programs according to an article in the Wall Street Journal.3
Microsoft disclosed a cyber incident that compromised senior executives’ email accounts; it too will set expectations for disclosures regarding cyber incidents.
Companies must now assess the latent business impact of cybercrime and materiality to report in order to meet new SEC requirements.
Phishing and Business E-mail Compromise.
When a targeted individual sees an email from someone they know, trust, and like the individual being targeted is more likely to open the e-mail, and that is what cyber attackers are counting on. Often the email may come from a legitimate sender who has had their email account access compromised, such as an individual at a state trade association, a CPA firm, or other known individuals. We’ve previously written about this type of attack (originally in January of 2021 Malicious Emails From People You Know, Trust and Like (bankonitusa.com), and the following page has some statistics from the F.B.I. on this type of attack. Business Email Compromise: The $50 Billion Scam (ic3.gov).
The cyber attackers’ goal is to transfer money out of your institution to an account that is controlled by the cyber attackers, typically organized crime. You and your clients may be at risk for this type of attack. The F.B.I. has a webpage that provides a description about Business Email Compromise and contains a few tips that are appropriate for sharing with customers here: Business Email Compromise — FBI.
Is Your Institution Using Social Media? Make Sure You Are Also Using Multi-Factor Authentication.
Financial Institutions utilize social media to connect with customers and prospects by providing informative and engaging content while celebrating the successes of their communities. However, it also attracts bad actors whose goal is to take advantage of your financial institution.
It’s a Reputational Risk for Your Institution.
Cyber attackers target financial institutions’ social media sites making posts with fake content, attracting visitors to click on malicious links, or holding the site hostage and demanding a ransom payment from the institution.
Utilizing Multi-Factor Authentication (MFA) tools offered by the social media sites where your institution has a presence can significantly reduce the risk of your institution becoming a victim.
This Nation Has a Bigger Hacking Program Than Every Other Major Nation Combined.
FBI Director Christopher Wray testified before the U.S. House China committee about intrusions into U.S. critical infrastructure networks by China’s hackers. The Director stated that China is not focused solely on political or military targets, but is also positioned across U.S. civilian infrastructure. He went on to say that the PRC has a bigger hacking program than every other major nation combined.2
Wray said the FBI is working in partnership with the private sector, allies abroad, and all levels of the U.S. government—especially the NSA [National Security Agency], Cyber Command, and CISA [the Cybersecurity and Infrastructure Security Agency], as well as ONCD [the Office of the National Cyber Director], to actively defend against the threats posed.
One Key to a Happy Marriage? A Joint Bank Account.
Newlyweds have plenty of decisions to make that could affect the trajectory of their marriage: where to live, division of household chores, and when and if to have children. This article from Kellogg School of Management at Northwestern University says that among the most important discussions is whether and how to merge their finances. One Key to a Happy Marriage? A Joint Bank Account. (northwestern.edu)
Too Long, Too Crowded, Too Much Lecturing & Not Enough Participation. 6 Tips to Make Online Meetings Better.
Research shows that participants are much less engaged in virtual meetings than when gathering in person. Face-to-face discussions activate our brains more, with increased eye contact, facial processing, and synchronized neural activity between individuals according to a study published by MIT Press.3 This article from The Wall Street Journal provides 6 tips for making online meetings more engaging and effective. 6 Ways to Make Your Online Meeting Better, More Engaging - WSJ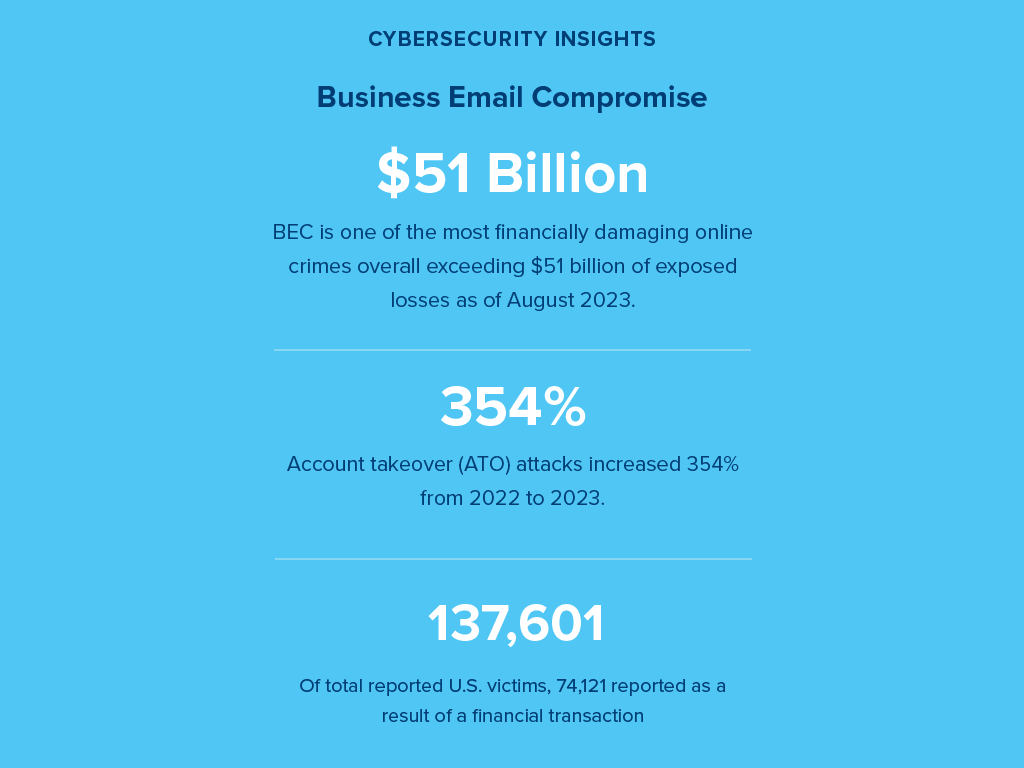
--
1 “Such a setup allows the attacker to steal and intercept the target’s password and the session cookie that proves their ongoing and authenticated session with the website. Note that this is not a vulnerability in MFA; since AiTM phishing steals the session cookie, the attacker gets authenticated to a session on the user’s behalf, regardless of the sign-in method the latter uses.” From cookie theft to BEC: Attackers use AiTM phishing sites as entry point to further financial fraud
2 “…we discovered that it took as little time as five minutes after credential and session theft for an attacker to launch their follow-on payment fraud. From our observation, after a compromised account signed into the phishing site for the first time, the attacker used the stolen session cookie to authenticate to Outlook online (outlook.office.com). In multiple cases, the cookies had an MFA claim, which means that even if the organization had an MFA policy, the attacker used the session cookie to gain access on behalf of the compromised account.” From cookie theft to BEC: Attackers use AiTM phishing sites as entry point to further financial fraud
3 Cyber Management Details Emerge Under SEC Rules


Submit your comment
Upon completion you will be automatically redirected to the electronic Authorized Resellers Agreement.